1. Arrange students into groups. Each group needs at least ONE person who has a mobile device.
2. If their phone camera doesn't automatically detect and decode QR codes, ask students to
4. Cut them out and place them around your class / school.
1. Give each group a clipboard and a piece of paper so they can write down the decoded questions and their answers to them.
2. Explain to the students that the codes are hidden around the school. Each team will get ONE point for each question they correctly decode and copy down onto their sheet, and a further TWO points if they can then provide the correct answer and write this down underneath the question.
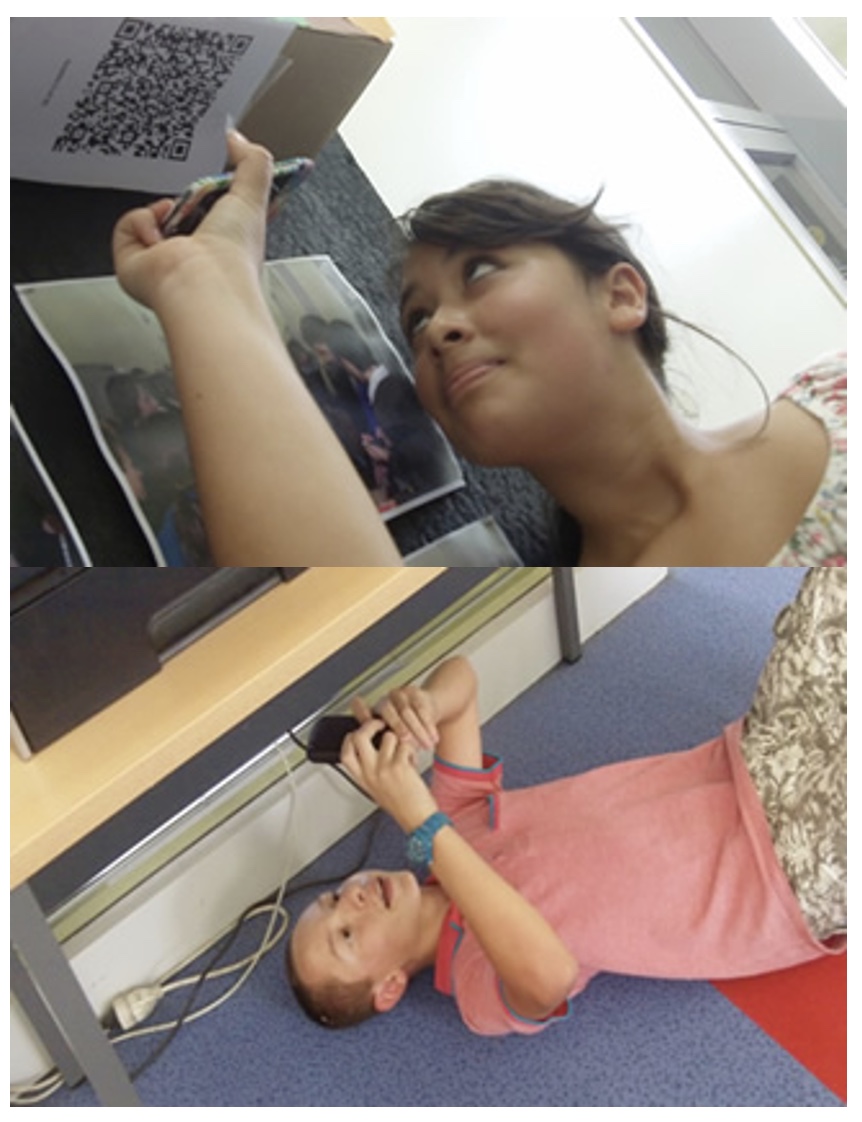
3. Away they go! The winner is the first team to return with the most correct answers in the time available. This could be within a lesson, or during a lunchbreak, or even over several days!
4. A detailed case study in how to set up a successful QR Scavenger Hunt using this tool can be found here.
Question | Answer |
| 1. User acceptance testing is often the final step before | What is User Acceptance Testing rolling out the application, uh, this gives the end user the who will be using applications confidence that the application will meet there requirements. This helps nail bugs related to usability of the application.... | 2. The goal of software testing is to cost effectively identify and communicate potential problems with the software as possible and iterate with the development team until the identified bugs are eliminated. The goal is consistent with the goal of the development team to provide high quality software that is free of errors to the end users | What is the goal of a software test | 3. Testing fits in by helping to reduce the chances of any errors or problems occurring during the actual performance | Where does Testing Fit In | 4. The UAP is generally presented to the consumer/ client in the form a terms and conditions. These terms and conditions are usually a long list of points and rules that you must abide by, it also states that you accept that the developer is not responsible for problems caused by the consumer. This type of terms and conditions can be found all over the place, when you install new software | What are the steps to follow with the ‘User Acceptance Process | 5. To ensure that the software is working properly as required by the user. | Why is Testing Important | 6. MS Project, Visio Gantt chart, Excel spreadsheet, Planning sheet | What Planning Techniques do we have | 7. To ensure hardware, software, data and people, are protected and safe. | Why do we need security | 8. To allow access to those who should have access whilst denying those that should not gain access. | List some Security Issues for physical security systems. | 9. Continuing fight with new encryptions and their solution. | List some Security Issues for logical security systems. | 10. Access is controlled by several stages of security. | What does ‘layered security’ mean | 11. Physical, Logical and personal. | Security Categories – list and describe | 12. Open Source, Single User, Multi – user license, Freeware | What Types of Software License are there | 13. Problems that cannot be solved are passed to a higher level technician. | What is an Escalation process | 14. To provide a professional auditable trail to support good customer support | Why do we need escalation procedures | 15. No. if the problem is simple and can be solved immediately | Do Escalation Processes apply in all cases | 16. CD/DVD, Download from site or Mirror, Memory Stick, Image | What methods of software loading do we have |

Question 1 (of 16)

Question 2 (of 16)

Question 3 (of 16)

Question 4 (of 16)

Question 5 (of 16)

Question 6 (of 16)

Question 7 (of 16)

Question 8 (of 16)

Question 9 (of 16)

Question 10 (of 16)

Question 11 (of 16)

Question 12 (of 16)

Question 13 (of 16)

Question 14 (of 16)

Question 15 (of 16)

Question 16 (of 16)